- PagerDuty /
- Integrations /
- Imperva Incapsula Integration Guide
Imperva Incapsula Integration Guide
Imperva Incapsula is a cloud-based application delivery service that protects websites and increases their performance, improving end user experiences and safeguarding web applications and their data from attack.
Through an application-aware, global content delivery network (CDN), Incapsula provides any website and web application with best-of-breed security, DDoS protection, load balancing and failover solutions—available as standalone services or as an integrated solution.
With the growing number of attacks targeting organizations worldwide, operations teams are under more pressure than ever to stay on top of the increasing number of incidents. By using PagerDuty, Imperva Incapsula customers can now better manage incident response. Incapsula's integration with PagerDuty gives your ops teams the tools they need to be more responsive to the growing volume of threats.
Getting Started
In PagerDuty
-
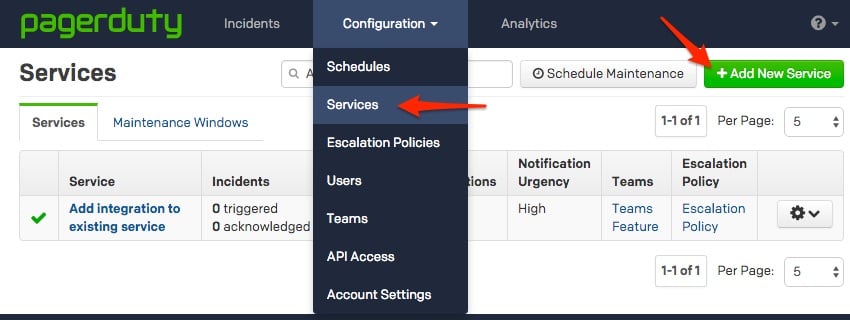
From the Configuration menu, select Services.
- On your Services page:
If you are creating a new service for your integration, click +Add New Service.
If you are adding your integration to an existing service, click the name of the service you want to add the integration to. then click the Integrations tab and click the +New Integration button.
-
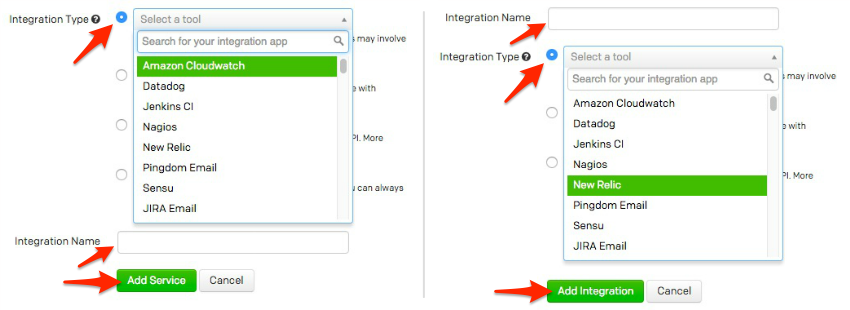
Select your app from the Integration Type menu and enter an Integration Name.
If you are creating a new service for your integration, in General Settings, enter a Name for your new service. Then, in Incident Settings, specify the Escalation Policy, Notification Urgency, and Incident Behavior for your new service.
- Click the Add Service or Add Integration button to save your new integration. You will be redirected to the Integrations page for your service.
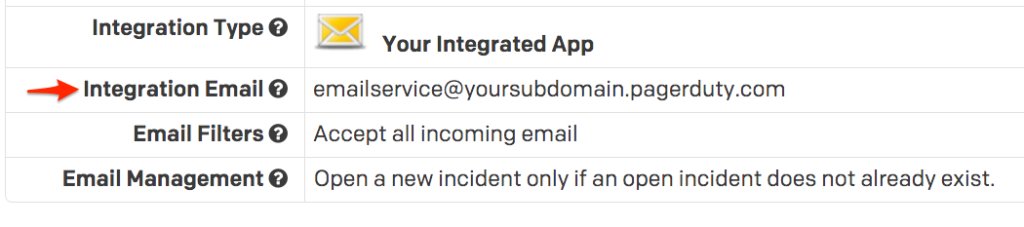
- Copy the Integration Email for your new integration:
-
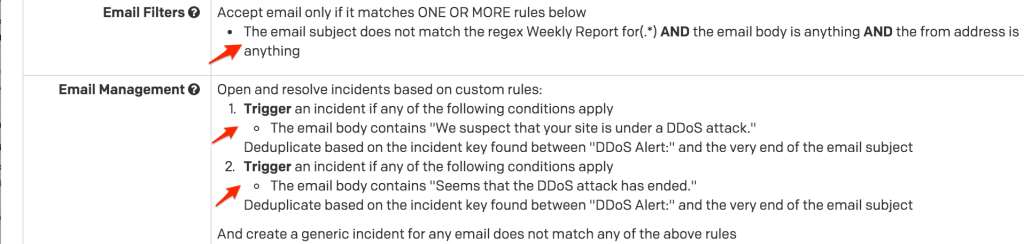
You can leave the PagerDuty configuration here to accept all emails from Incapsula, or you can create email rules to filter out non important issues and automatically resolve alerts when Incapsula detects that an issue is resolved. In the below example, the Email Filters section was used to only accept emails which do not match the regex:
Weekly Report for(.*) -
This will filter out weekly report emails, which don't represent an urgent issue and shouldn't wake up on-call users. If desired, you can create rules on a second service to accept these emails and either alert a different escalation policy, or alert your existing escalation policy using low-urgency notification rules.
In the Email Management section, custom email parsing rules were created to trigger an incident if the email body contains
We suspect that your site is under a DDoS attackand to resolve the same incident if the email body containsSeems that the DDoS attack has ended. The incident key is set on both the trigger and resolve rules to match all text that followsDDoS Alert: -
Now, when Incapsula detects an issue and sends a notification to your service email address, you'll see the email appear as an incident in PagerDuty. If you've configured trigger/resolve rules, you'll see these incidents automatically resolve when an email matching your resolve rule is sent from Incapsula to your PagerDuty service.
FAQ
Can Incapsula create PagerDuty alerts for conditions other than DDoS attacks?
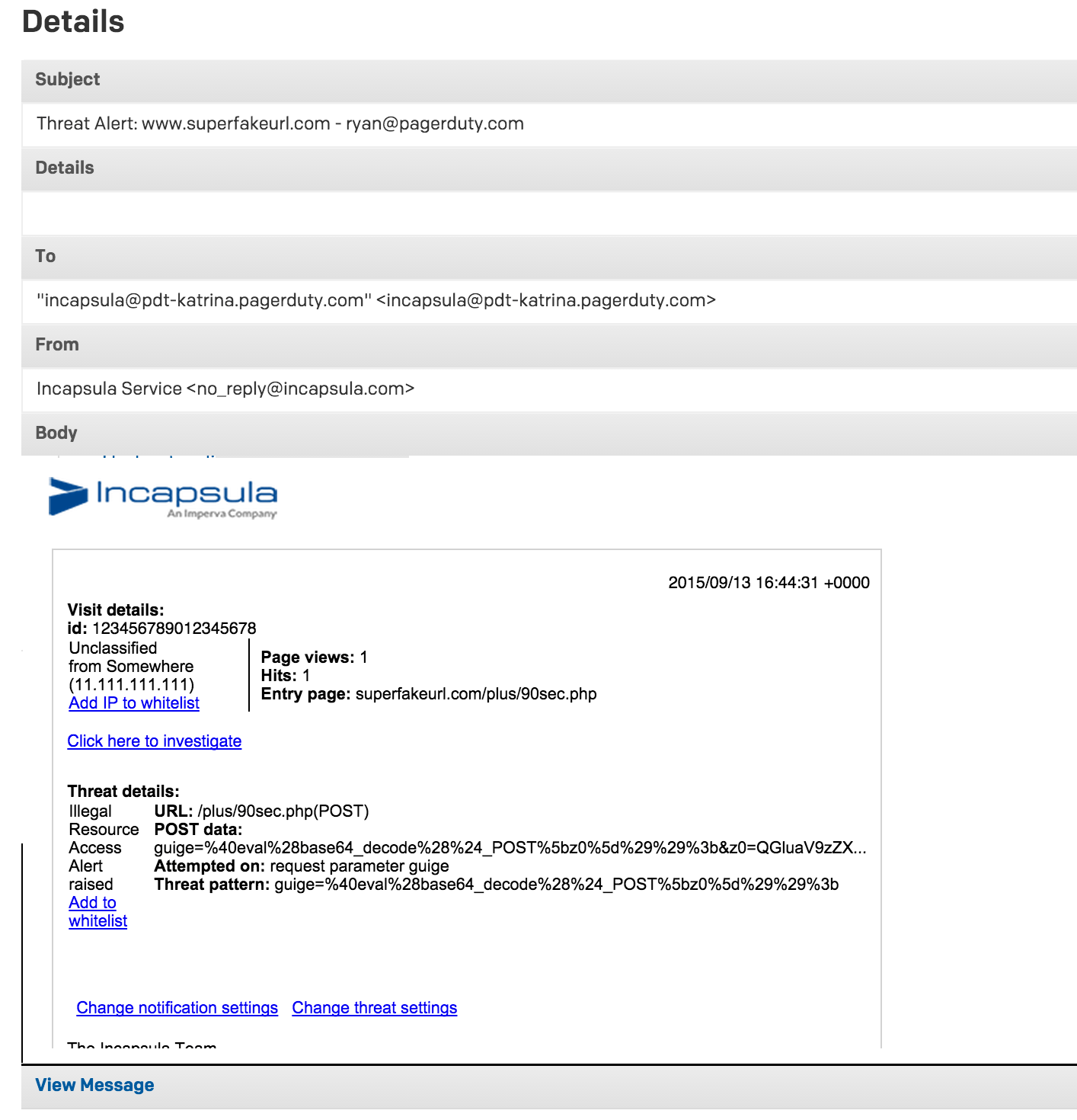
Yes! You can trigger/resolve rules for any alert that Incapsula can send a notification on: SQL injection, cross site scripting, remote file inclusion, and illegal resource access request blocks are just some of the possibilities. You'll just need to make sure that your service contains trigger and resolve rules which match information contained somewhere in the email Incapsula sends for that alert, and that you set an incident key based on information contained in both your trigger and resolve emails to match the incoming emails to each other correctly.
Ready to get started?
Try any product on the Operations Cloud for free.
No credit card required.