- PagerDuty /
- Integrations /
- RSA Security Integration Guide
RSA Security Integration Guide
RSA Security allows you the ability to protect your business with products and solutions that help mitigate risk, increase information-security and governance, and remain compliant with security standards. With RSA you can detect, investigate, and remediate incidents with unprecedented precision and speed. RSA coupled with PagerDuty allows you to be automatically alerted when these incidents occur to reduce the amount of time it takes to resolve these incidents.
In RSA:
-
-
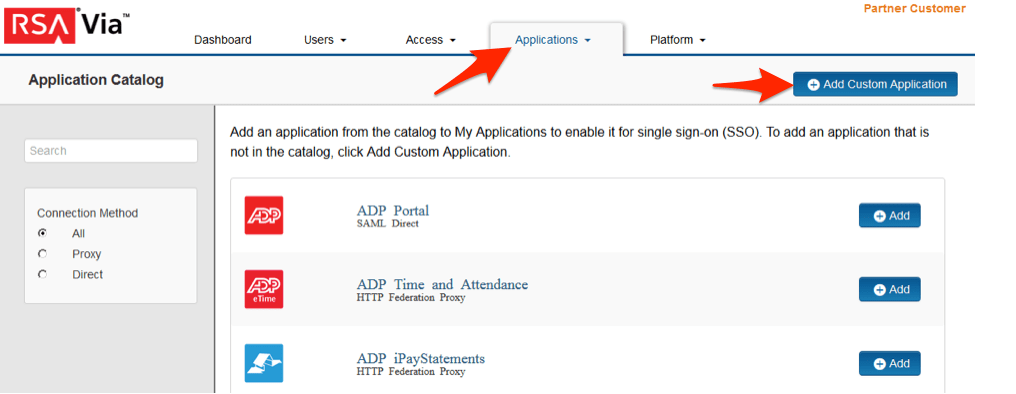
In the RSA Via Access Administration Console, click the Applications tab, then click the + Add Custom Application button.
-
From the list of applications, click +Add for the application that you wish to add. To add an application that is not in the list, click +Add Custom Application.
-
On the Basic Information page, specify the application name and click Next Step.
-
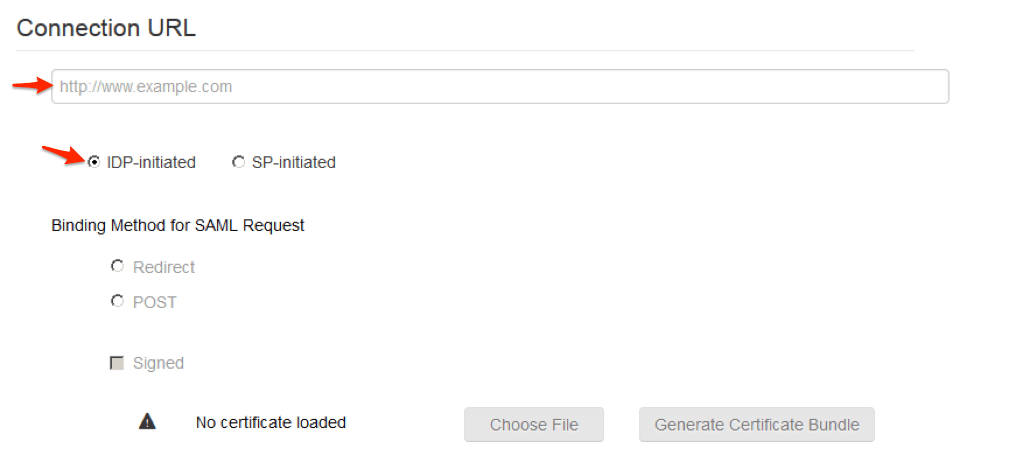
Note: The following IDP-initiated configuration works for both IDP-initiated and SP- initiated connections.
-
On the Connection Profile page, choose IDP-initiated and leave the Connection URL blank.
-
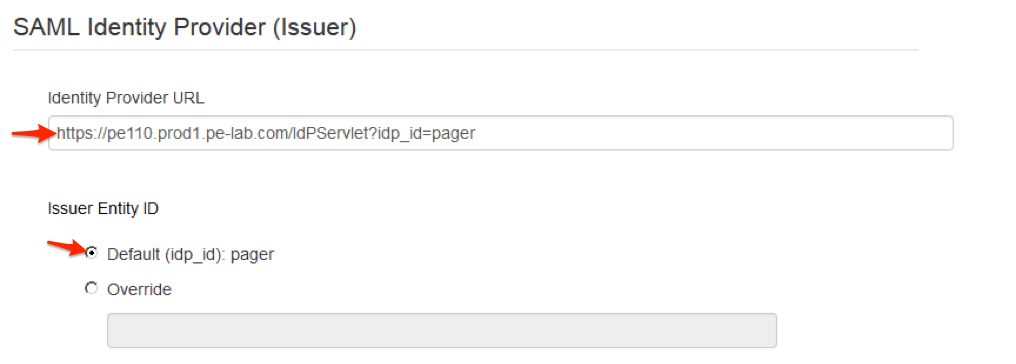
Scroll down to SAML Identity Provider (Issuer)
-
Take note of the Identity Provider URL it will be needed later to configure PagerDuty.
-
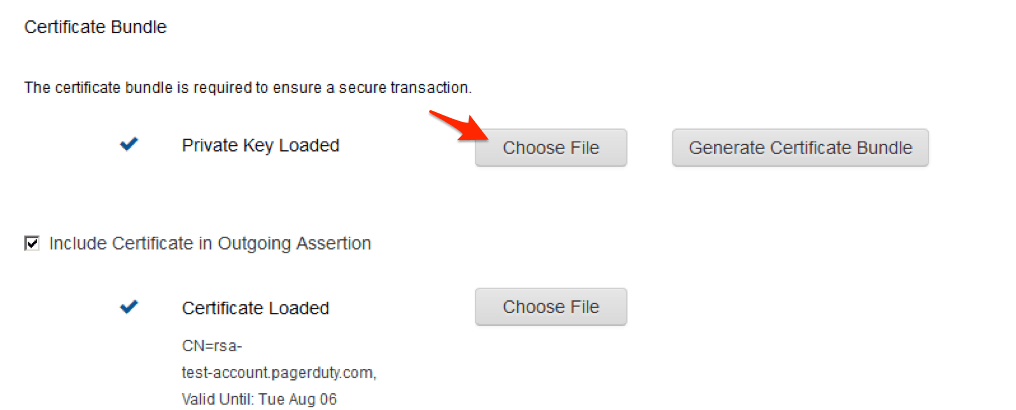
Click Choose File and upload the RSA Via Access private key.
-
Select the checkbox Include Certificate in Outgoing Assertion.
-
Click Choose File and upload the cert.pem public certificate.
-
Scroll down to the Service Provider
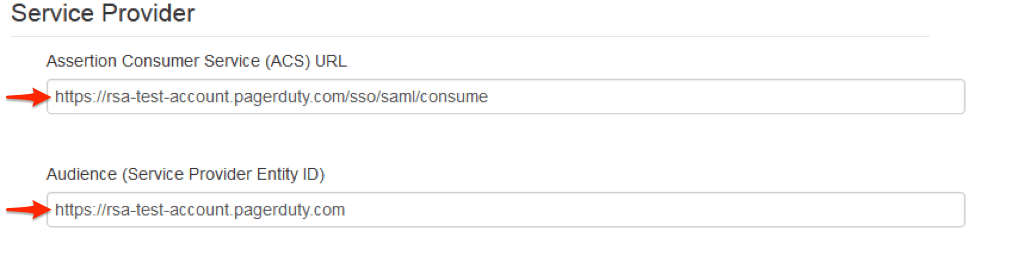 a. In the Assertion Consumer Service (ACS) URL field, enter https://<your_instance>.pagerduty.com/sso/saml/consume b. In the Audience (Service Provider Entity ID) field, enter https://<your_instance>.pagerduty.com
a. In the Assertion Consumer Service (ACS) URL field, enter https://<your_instance>.pagerduty.com/sso/saml/consume b. In the Audience (Service Provider Entity ID) field, enter https://<your_instance>.pagerduty.com -
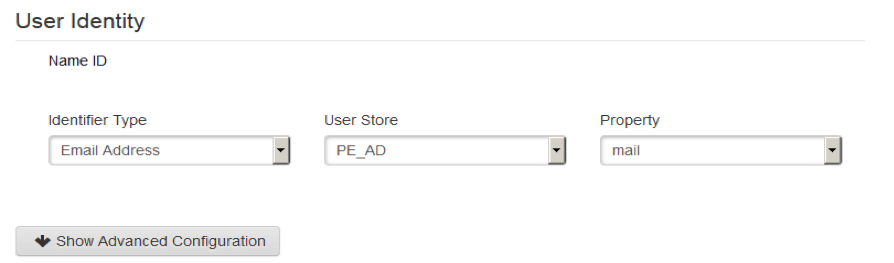
Scroll down to the User Identity Set the Identifier Type to Email Address and Property to mail.
-
Click Next Step.
-
On the User Access page, select the desired user policy from the drop down list.
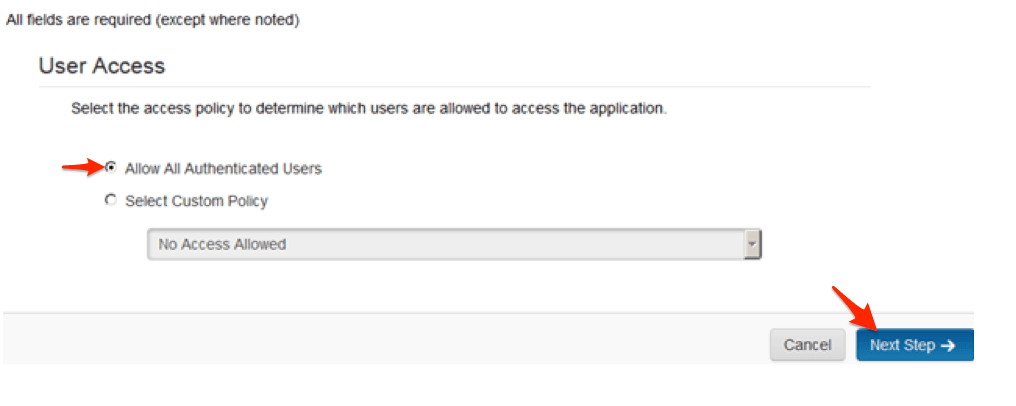
-
Click Next Step.
-
On the Portal Display page, select Display in Portal.
-
Click Save and Finish.
-
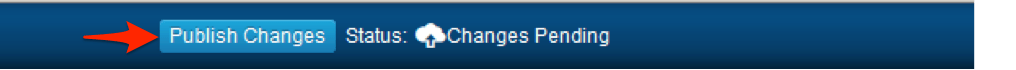
Click Publish Changes. Your application is now enabled for SSO.
In PagerDuty:
-
In your account, under the Configuration tab, select Account Settings from the dropdown menu.
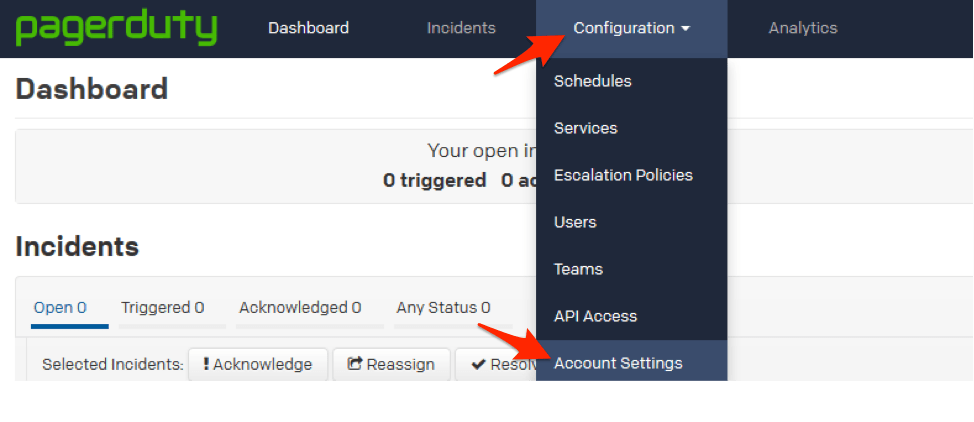
-
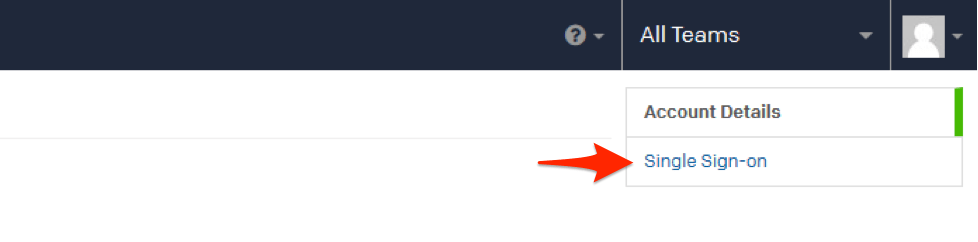
Select the Single Sign-on tab on the right-side of the page.
-
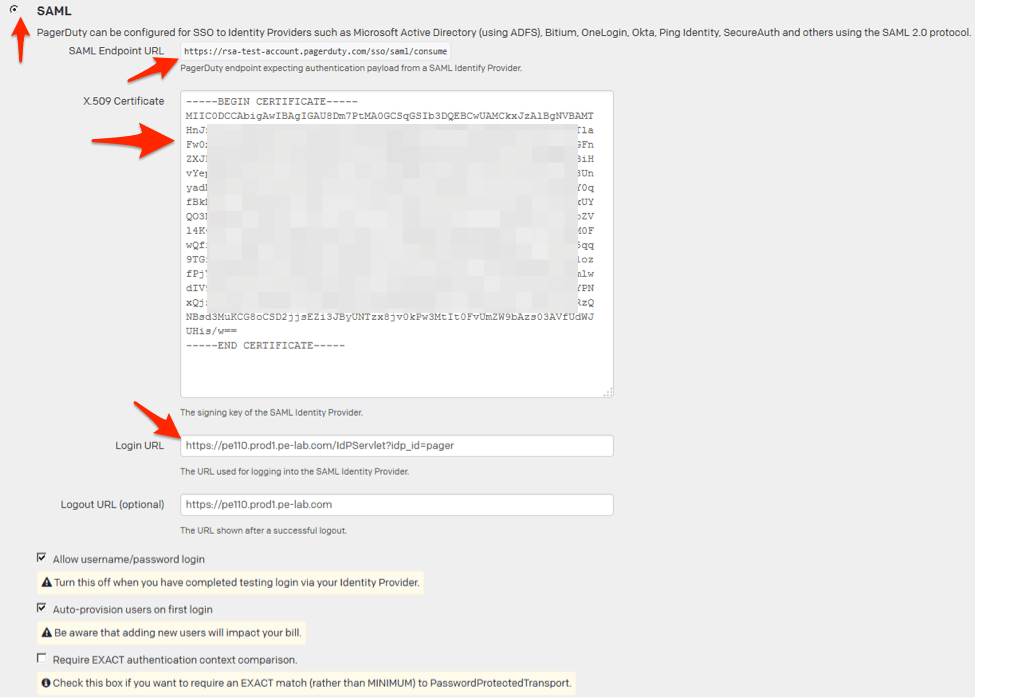
Select the SAML radio button.
-
Take note of the SAML Endpoint URL, this is the ACS URL on the RSA Via Access.
-
Paste the RSA Via Access 509 certificate into the window including the ---Begin and End lines.
-
Enter the Identity Provider URL from step 6 into the Login URL field.
-
If you would like the users to still be able to login with their username and password that is not managed by RSA Via Access then check Allow Username/password login.
-
Manually configure a user or check the Auto-provision users on first login.
-
Click Save Changes.
Ready to get started?
Try any product on the Operations Cloud for free.
No credit card required.